Peta ransomware (Removal Guide) - Sep 2019 update
Peta virus Removal Guide
What is Peta ransomware?
Peta is an advanced cryptovirus that modifies computer system to prevent victims from visiting security-related sites
Peta is a ransomware developed by hackers who are responsible for the release of one of the most notorious file locking malware families in the wild – Djvu/STOP. Ransomware[1] is a devastating type of infection that not only modifies how the Windows system works but also encrypts all personal files located on the local or networked hard drive. To retrieve access to the data, victims of the Peta file virus are asked to pay a ransom of $980 or $490 in Bitcoin cryptocurrency.
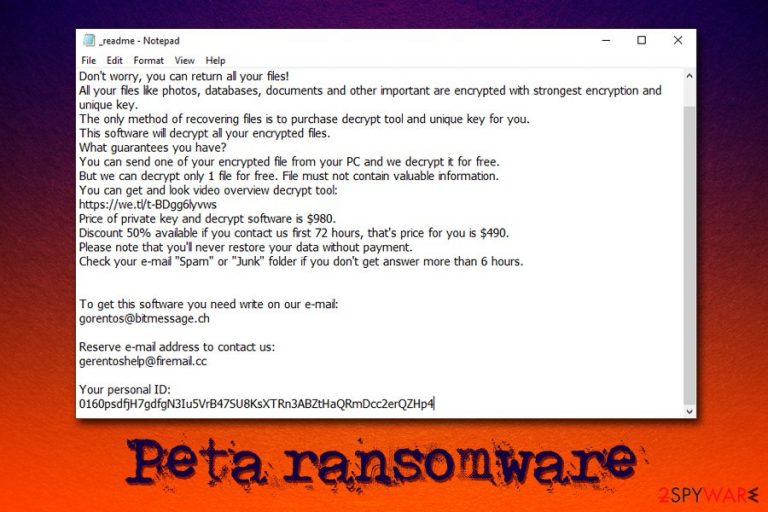
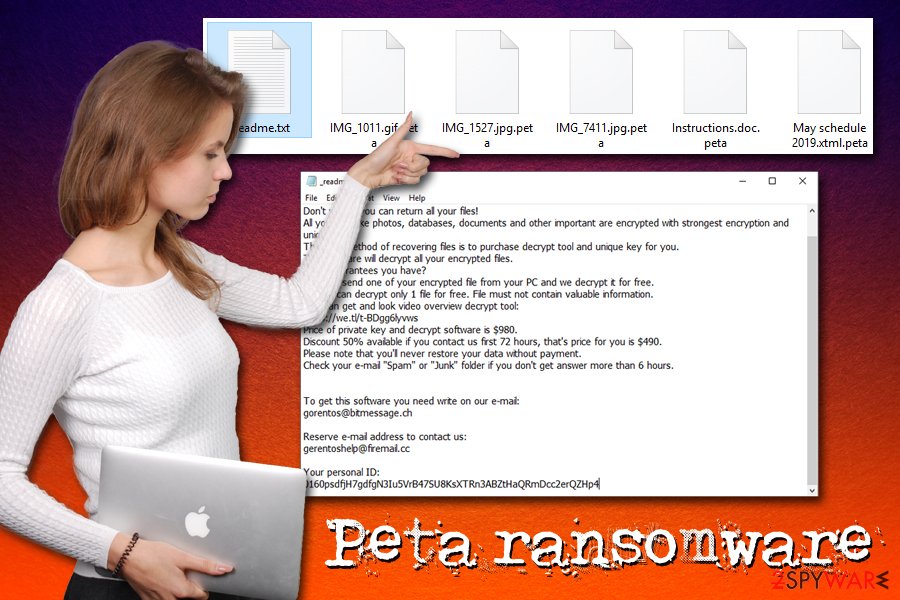
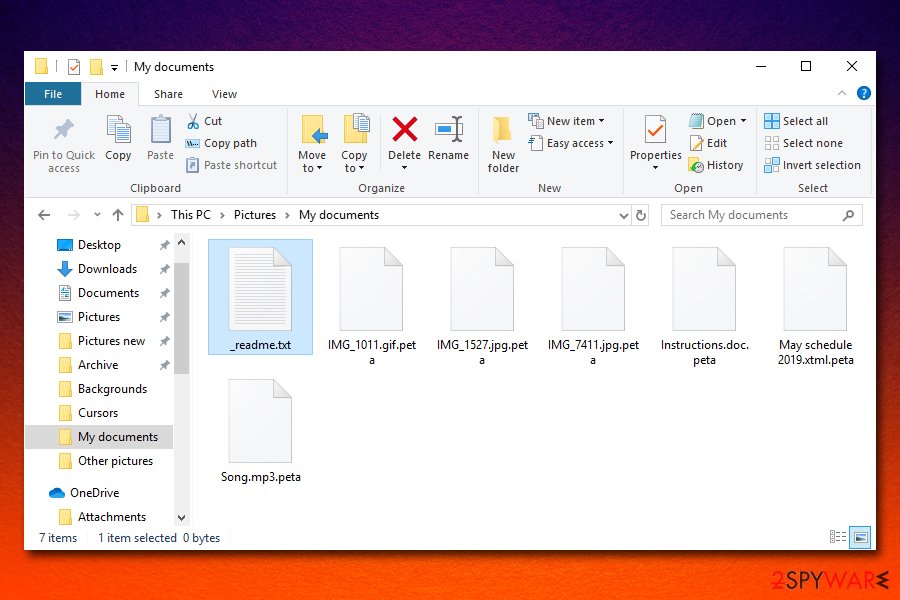
Besides encrypting pictures, videos, music, database, document and appending .peta file extension, Peta virus also drops a ransom note _readme.txt – the name of the note and the body text does not differ from many other Djvu variants, such as Seto, Gero, Nacro, and many others. Even contact emails gorentos@bitmessage.ch and gerentoshelp@firemail.cc were already used by hackers before.
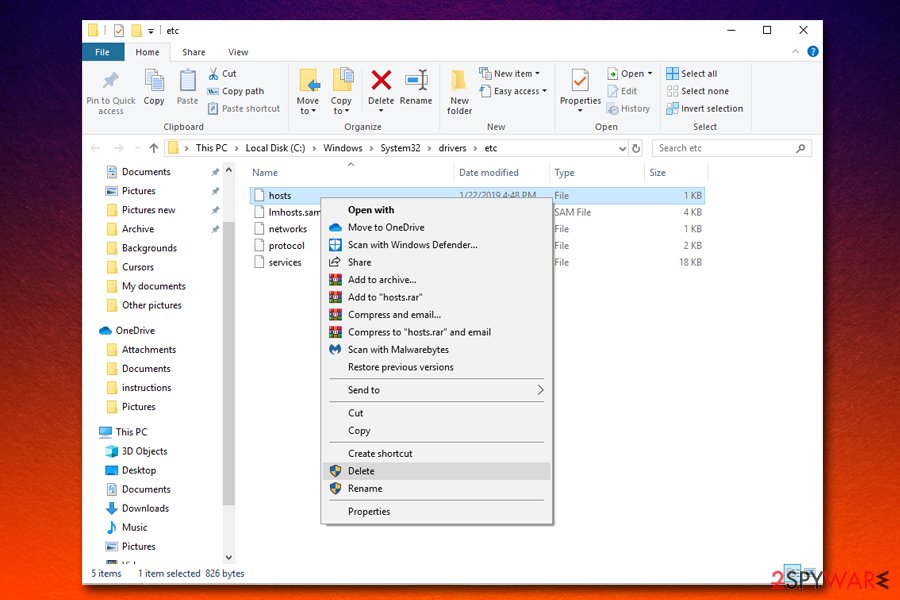
Peta ransomware, along with dozens of other variants is capable of modifying hosts file that prevents users from accessing cybersecurity sites. After virus termination, victims need to delete this file located in C:\Windows\System32\drivers\etc and change all their passwords to ensure no account compromise.
| Name | Peta ransomware |
| Type | Cryptovirus |
| Family | STOP/Djvu |
| Ransom note | _readme.txt |
| Contact | gorentos@bitmessage.ch or gerentoshelp@firemail.cc |
| File extension | .peta |
| Ransom size | $980 or $490 |
| File decryption | Only available via backups, third-party software, or might be possible via paid Dr.Web service |
| Virus elimination | Scan your machine with reliable anti-malware software in Safe Mode |
| Recovery | To avoid unexpected system errors and other troubles after a virus infection, use FortectIntego |
While previous versions of this notorious ransomware family were in some cases possible to decrypt using a free tool from security researchers, Peta ransomware now possesses improved functionality that prevents the decryptor from working.
Nevertheless, experts[2] advise avoiding paying the ransom, as cybercriminals might scam you or send a malicious executable in return. Besides, you can try using third-party recovery tools after Peta removal to retrieve at least some of the locked files. We provide all the relevant instructions at the bottom of the article, so make sure you check them out.
Peta ransomware can be distributed in a variety of methods, such as:
- Fake updates;
- Spam emails;
- Software cracks;
- Exploits;
- Web injects;
- Remote Desktop;[3]
- Backdoor, etc.
As soon as Peta ransomware reaches the machine, it locks all files on it and drops the following ransom note which also offers users a test decryption service (another trick to make users provide a false sense of certainty):
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-BDgg6lyvws
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gerentoshelp@firemail.ccYour personal ID:
0160psdfjH7gdfgN3Iu5VrB47SU8KsXTRn3ABZtHaQRmDcc2erQZHp4
Another reason to remove Peta ransomware is due to its functionality – some of the variants are capable of harvesting sensitive data (like login details and banking information), modifying hosts file and even proliferating a secondary payload such as AZORult Trojan. Due to hosts file modification, you will not be able to reach any security-related websites, including 2-spyware.com.
To get rid of Peta virus, you will have to scan your machine with reputable security software. After that, you can attempt to recover files using the instructions in the recovery section below. Finally, you should consider using FortectIntego to repair damage done to Windows system files.
User comprehensive protection to ensure no ransomware can compromise your files in the future
Ransomware victims are mostly those who have never been infected with such a devastating virus before – that explains a high infection rate over the world. Many users disregard the security precautions that should be taken to reduce the chance of malware infection to a minimum, as most of the infiltrations are triggered by users themselves, whether it is due to lack of knowledge or negligence.
The first step to a safer machine is adequate applications, such as anti-malware software, ad-blocking apps, as well as Firewall. A subsequent step is to make sure that all the software and the operating system is patched with the latest security updates that prevent vulnerabilities from being used to install the payload automatically.
Finally, users should simply be more careful and critical when browsing the web: never download software cracks, use strong passwords (and never re-use them), never open macro-induced spam email attachments, etc.
Nevertheless, no method is 100% secure, and the infection is still possible. To avoid the treacherous ramifications of ransomware, you should make sure that you backup your most important files either on an external device or a remote virtual drive.
Get rid of Peta ransomware and delete the hosts file to recover from the infection
While most of the ransomware delete themselves as soon as they perform the encryption process on the host computer, Peta virus might leave malicious modules that keep stealing sensitive data and encrypt all the incoming files. Therefore, it is vital to make sure that a full Peta removal is performed. For that, use powerful anti-malware software to scan your computer thoroughly. If the malware is tampering with your security application, access Safe Mode with Networking – the secure environment will temporarily disable the function of the virus.
Once you remove Peta ransomware, you need to perform the following tasks:
- Change the passwords of all accounts (make them relatively long and use symbols and capital letters)
- Check your bank account and make sure no unauthorized transactions were performed; if yes – contact your bank immediately;
- Go to the following location on your computer: C:\Windows\System32\drivers\etc. Delete the “hosts” file using admin permissions.
Finally, you can attempt to recover .peta locked files. While STOPDecrypter will not work, you can ask Dr.Web for help, employ third-party software, or using Windows Previous Versions feature.
Getting rid of Peta virus. Follow these steps
Manual removal using Safe Mode
The best way to get rid of Peta file virus is by entering Safe Mode with networking and performing a full system scan:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Peta using System Restore
System Restore can also be useful when trying to eliminate the virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Peta. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Peta from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Peta, you can use several methods to restore them:
Data Recovery Pro might be able to retrieve at least some of your files
Data Recovery Pro looks for copies of your files on the HDD/SSD and, if space was not overwritten yet, it could recover a healthy and usable file back. If the previous file location was already erased, recovering it will be impossible.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Peta ransomware;
- Restore them.
Windows Previous Versions feature might be a solution for you
If you were prepared and had System Restore enabled before Peta ransomware attacked you, you should be able to retrieve each of the files individually by using this method.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Make use of ShadowExplorer
In case the cryptovirus failed to delete Shadow Volume Copies you are in luck – ShadowExplorer should retrieve all your files without any problems.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Make use of Dr.Web decryption service
Dr.Web is a security company that is known to be able to decrypt several variants of STOP/Djvu ransomware. However, the service is not free – the Rescue pack costs €150, and the only type of files that might be restored are MS Office documents and PDF files.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Peta and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Bojana Dobran. 27 Terrifying Ransomware Statistics & Facts You Need To Read. PhoenixNAP. The most modern data center.
- ^ Novirus. Novirus. Security researchers' advice from the UK.
- ^ Jakub Křoustek. Ransomware attacks via RDP choke SMBs. Avast. Official security blog.







