SystemCyberspace Mac virus (Tutorial)
SystemCyberspace Mac virus Removal Guide
What is SystemCyberspace Mac virus?
SystemCyberspace is a type of malware that can steal data and install additional malicious extensions
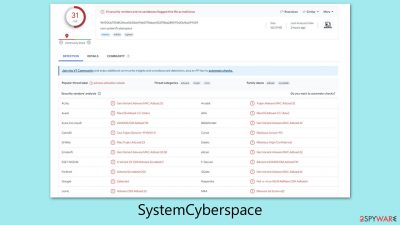
SystemCyberspace is a deceptive program that often gets installed on Mac computers without the user's awareness, typically through misleading Flash Player updates or pirated software downloads. It is a member of the Adload malware family, notorious for its aggressive targeting of Mac systems and its ability to secretly install additional harmful payloads.
Once installed, this malware secures elevated privileges to implant various malicious files, significantly enhancing its persistence and making removal efforts difficult. Eradicating the virus often results in its reappearance after a computer reboot.
A clear indication of the SystemCyberspace virus infection is the alteration of web browser settings. Affected users might notice a new extension, marked by a magnifying glass icon on a gray background. This extension can change homepage settings and redirect search queries.
The main purpose of this malware is to generate income through the display of unsolicited ads. This leads to an increased presence of pop-ups, promotional offers, and suspicious links during internet browsing. Additionally, it can show phishing messages and misleading alerts, posing further risks to online safety.
| Name | SystemCyberspace |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Fake Flash Player installers, illegal software bundles |
| Symptoms | Installs a new extension and application on the system; changes homepage and new tab of the browser; inserts ads and malicious links; tracks sensitive user data via extension |
| Removal | You can remove Mac malware with the help of powerful security tools, such as SpyHunter 5Combo Cleaner or Malwarebytes. We also provide manual removal steps below |
| System optimization | After you terminate the infection with all its associated components, we recommend you also scan your device with FortectIntego to clean your browsers and other leftover files from the virus |
Spreading techniques
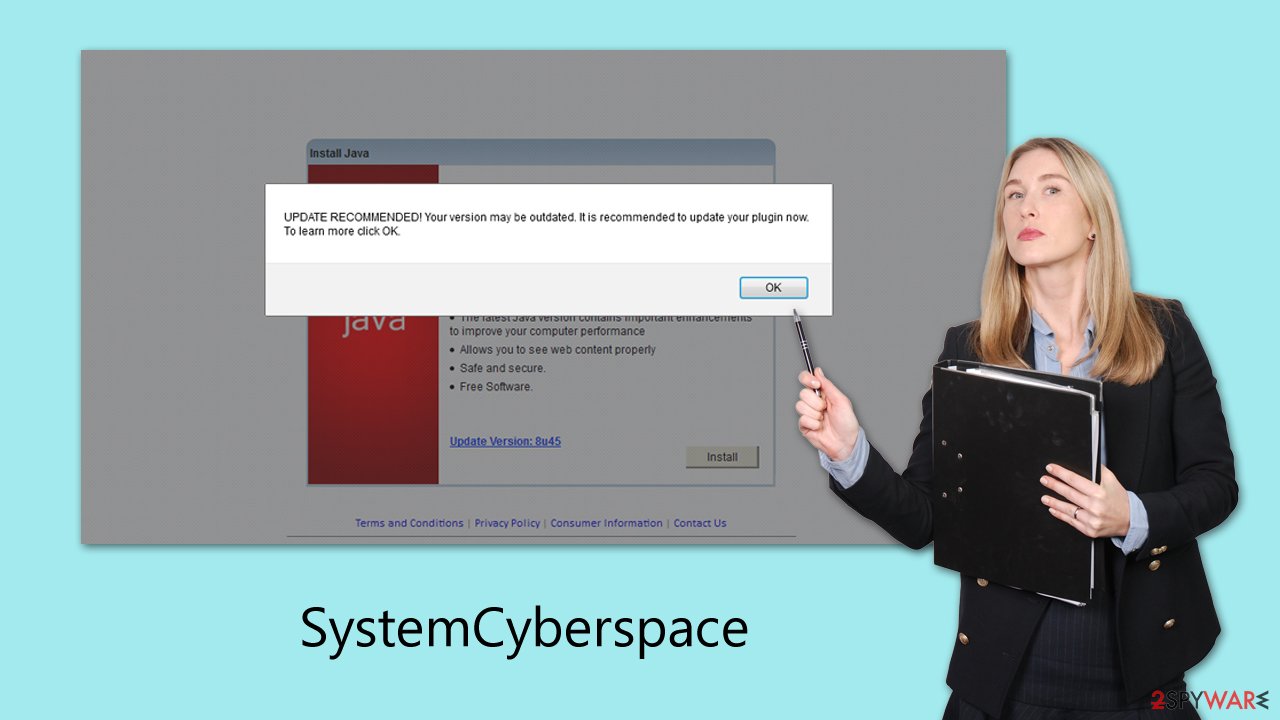
Adload malware family, known for targeting Macs, includes various variants such as EngineOfflineAlgorithm, WouldLatest, and NavigateEngine. Its widespread impact is largely due to an effective distribution method. Key to its distribution are counterfeit Adobe Flash Player installers, often sourced from unreliable websites or via email attachments.
These installers, disguised as legitimate Adobe software, are misleading as Adobe has already discontinued Flash Player. Any prompts for Flash downloads are, therefore, deceptive
Another significant avenue for Adload's spread is through torrents and cracked software. Here's how it works:
- Torrents enable peer-to-peer file sharing, where users directly exchange files.
- Cracked software is illegal modifications that bypass security and licensing restrictions.
- Malware risk escalates when users download these cracked versions, especially if they ignore security software alerts.
To protect against malware, one should download software only from trusted sources and be wary of unexpected emails or messages with links or attachments. Running anti-malware software on Macs, keeping software and operating systems up to date, and staying alert to unusual browser activities like new extensions, pop-ups, and redirections are crucial defensive measures. Recognizing and acting upon these signs can greatly enhance your digital safety.
Operational principles
Upon infection, the SystemCyberspace virus swiftly alters major web browsers like Safari, Google Chrome, or Mozilla Firefox. The most evident change is the homepage, often replaced with a site like Safe Finder, another malicious entity targeting Mac users. This modification is part of the virus's strategy to monetize through advertisements.
As a result, search queries are often rerouted, leading to unexpected results. The virus may set a different default search provider, such as Bing or Yahoo, and the top search results are frequently cluttered with ads. Clicking on these links can be hazardous, as they might lead to websites harboring additional viruses or promoting fake services.
Beyond these intrusive browser changes, the SystemCyberspace virus poses significant privacy and security threats. It installs itself with high-level permissions, enabling it to freely use AppleScript and evade Mac's built-in defenses like XProtect. This capability allows the malware to monitor users' browser activities extensively, including capturing sensitive information like passwords, account details, and credit card numbers. Therefore, it's crucial to avoid sharing any important information on the infected device due to the severe privacy risks involved.
SystemCyberspace removal steps
Removing malware from your device, particularly when dealing with resilient threats like Adload on Macs, requires careful consideration. It's generally recommended to avoid manual removal due to the complexity and persistence of this malware. Adload's use of built-in scripts complicates its elimination and often leads to its resurgence.
For most users, utilizing specialized automatic removal tools, such as recommended security applications SpyHunter 5Combo Cleaner or Malwarebytes, is the preferred method. These tools can circumvent the malware's tactics that typically hinder Mac's native security features, ensuring a more thorough removal and preventing future infections.
If you still choose to proceed with manual SystemCyberspace removal, be aware that it may not be entirely effective. The risk of the infection returning is significant if all malicious components aren't completely removed. However, regardless of whether you opt for automatic or manual removal, a critical step is to thoroughly cleanse your browsers. Detailed instructions for this are provided towards the end of the guidelines. This browser cleaning is vital to ensure that no traces of the malware remain in your system.
Upon infiltrating a system, the virus initiates its harmful activities by activating background processes whenever it operates. To effectively remove the core application of the virus, it's crucial to first halt these processes. This can be done by using the Activity Monitor on your Mac. Here, you should identify and terminate all processes related to the virus, ensuring they are no longer running.
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to adware and use the Force Quit command to shut them down
- Go back to the Applications folder
![Uninstall from Mac 1 Uninstall from Mac 1]()
- Find the virus name in the list and move it to Trash.
The PLIST files are small config files, also known as “Properly list.” They hold various user settings and hold information about certain applications.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
When the virus infiltrates, it will create new user profiles and login items to ensure continued presence. This is likely why you are unable to remove the application or extension from your system.
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
In the final stage of the removal process, addressing the changes made to your browsers is crucial. This involves removing the extension component that the virus may have installed. However, in some cases, direct SystemCyberspace extension removal might not be possible. If you encounter such a scenario, resetting the browser to its default settings is the alternative solution. This step ensures that any changes or additions made by the virus are completely eradicated.
For cleaning cached files and other residual data that the virus may have left behind, you can utilize a maintenance tool like FortectIntego. This app is designed to automate the cleaning process, making it more efficient and thorough. If you prefer to proceed manually, there are also step-by-step instructions provided below.
These manual steps will guide you through clearing the cache and other temporary files that could harbor remnants of the virus. Whether you choose the automatic tool or the manual method, ensuring your browsers are completely clean is a vital part of fully securing your system post-infection.
Getting rid of SystemCyberspace Mac virus. Follow these steps
Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.












