.wcry file extension virus (Removal Instructions) - May 2017 update
.wcry virus Removal Guide
What is .wcry file extension virus?
.wcry file extension warns about hazardous cyber infection
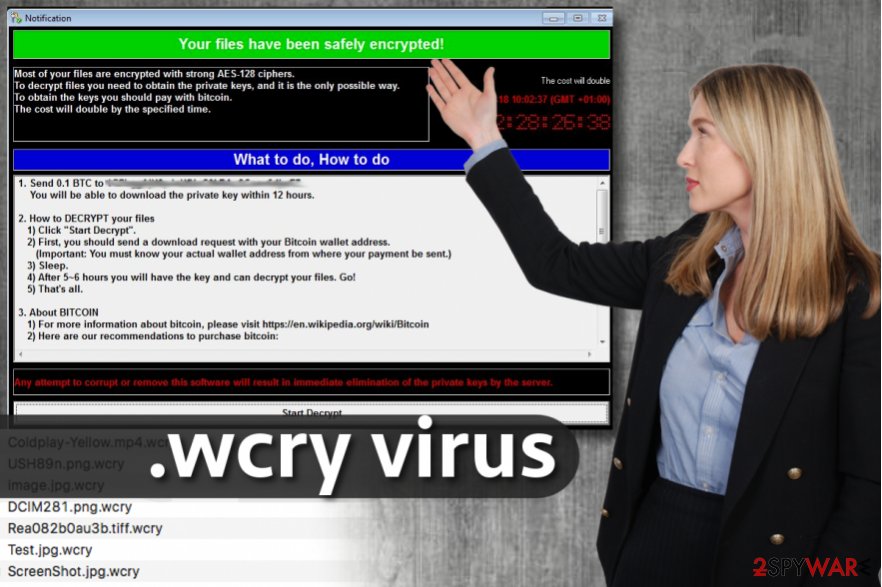
.wcry file extension virus is a file-encrypting malware that is also known as WannaCry, WanaCrypt0r, Wana Decrypt0r, WanaCrypt0r 2.0 and WannaCryptor. Ransomware has been spotted in February 2017. Then it was using an AES-128 encryption algorithm to corrupted files on the attacked computer and appended. wcry file extension to each of them. Following data encryption, it also delivered a ransom-demanding message where cyber criminals asked to pay 0.1 Bitcoin for data recovery. However, the virus was updated and on May 12, 2017, cyber criminals launched a massive worldwide attack.[1] Malware has already infected more than 200 thousand devices and swindled about $50 000.[2]. However, the number of the attacks is expected to grow, as well as the size of the ransom. Cyber criminals asked to pay $300; however, after few days the ransom increased up to $600. Though, if you have suffered from this cyber threat, you should not reach your credit card or think who can lend you some money. The most important task right now is .wcry virus removal. Malware not only can encrypt files but install other malware as well. Thus, do not hesitate and run a full system scan with professional malware removal program, such as FortectIntego.
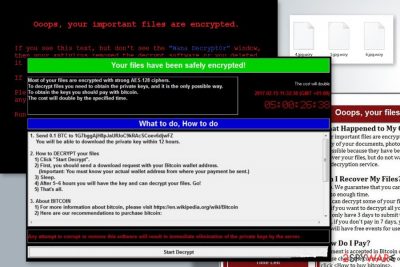
There is no way to stop ransomware[3] viruses once they start the encryption procedure because such programs finish their job very quickly[4]. You might notice a system slowdown, or you might not – typically ransomware doesn’t draw victim’s attention or raise any suspicion during the encryption procedure. As soon as data encryption is over, .wcry file virus displays a notification window which says:
Your files have been securely encrypted!
Most of your files are encrypted with strong AES-128 ciphers.
To decrypt files you need to obtain the private keys, and it is the only possible way.
To obtain the keys you should pay with bitcoin.
The cost will double by the specified time.
The described program window includes a countdown clock that shows time until the next ransom price raise. Below, there is a “What to do, How to do” table, which explains that the victim should send 0.1 BTC (which is approximately 100 USD) to a specified Bitcoin wallet. According to this ransom note, the victim should get access to the decryption tool within 12 hours. If you’ve been hit by .wcry ransomware, we suggest you remove the virus and not pay the ransom. The criminals might never respond to your transaction[5], and you might never see your files again (unless you have a backup, of course). Thus, you should remove .wcry file extension virus and protect from further cyber infections. Once you do that, you could restore files from backups. At the moment, backups are the only one solutions to rescue your files for free. However, you should not give up and try alternative data recovery options. Hopefully, they will help to restore at least some of your files.
Ransomware distribution techniques
When .wcry Trojan has been discovered, it was spreading via malicious email attachments. Thus, users were advised to be aware of scammy email letters that scammers prepare precisely. They often try to pretend to be trustworthy individuals who ostensibly work for big companies like Amazon or Paypal, however, invoices and payment confirmations they send typically contain malware, so we suggest you double-check sender’s email before opening the email or files attached to it. Some ransomware viruses that are slightly more sophisticated, (for example, Spora or Cerber) are distributed using advanced tools such as exploit kits. To protect yourself, install a reputable anti-malware program on the PC system. We strongly recommend you to keep clear of Internet sites that you know nothing about. Do not be tempted to click on clickbait article titles, catchy ads and be extremely careful when some suspicious site tries to convince you to install a program or an update. Chances are, you will be infected with malware all of sudden.
However, since the middle of May malware employed a new distribution and infiltration strategy. Currently, it takes advantage of a vulnerability in Microsoft Windows and spreads malware with the help of EternalBlue exploit. [6] The shady hacker group called “Shadow Brokers” have stolen this spying tool from National Security Agency (NSA). Cybercriminals took advantage of this leak and used this tool to target the CVE-2017-0145 vulnerability in Windows OS. Users are warned to update the operating system, as well as all software installed on their devices. This flaw has been already patched by Microsoft and updates are available even for users who still use Windows XP, Windows 2003, Windows 7, and Windows Server 2008 systems. Thus, you should install such updates immediately.
The safe way to remove .wcry file extension virus
After ransomware attack, we highly recommend you not to pay the ransom and remove .wcry virus right now – this way, you will secure your computer from further malware attacks because you can never know what else this virus can do. The latest versions of ransomware are known for being capable of installing other malware on the device. Considering how dangerous ransomware viruses are, we recommend you to use anti-malware program for .wcry removal. If you need advice what program to use, we suggest choosing one of these: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. A complete guide on how to uninstall ransomware is provided below this post.
Getting rid of .wcry virus. Follow these steps
Manual removal using Safe Mode
Please carefully read these instructions before you do anything. If you have any questions, ask them before you begin the virus elimination procedure.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .wcry using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .wcry. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove .wcry from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.In case of ransomware attack, all files (or at least the vast majority of them) can be recovered from a backup. That is why we always advise computer users to create them. If you do not have a backup, you can try these data recovery methods. Besides, this ransomware virus wasn't analyzed completely yet, so currently we cannot deny that it is possible to crack this virus and create a free decryption tool.
If your files are encrypted by .wcry, you can use several methods to restore them:
Use Data Recovery Pro
Install Data Recovery Pro using instructions provided below and scan your system for corrupted files. This program will try to restore them.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by .wcry ransomware;
- Restore them.
Use ShadowExplorer
ShadowExplorer checks whether Windows Volume Shadow Copies are on the system or not. If the virus deleted them, it means you won't be able to use them to recover your files. If it didn't delete them, you can use them to restore corrupted files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .wcry and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Dawn Kawamoto. 'WannaCry' Rapidly Moving Ransomware Attack Spreads to 74 Countries. Dark Reading. Cyber security's comprehensive news site.
- ^ Arjun Kharpal. Hackers who infected 200,000 machines have only made $50,000 worth of bitcoin. CNBC. Stock Markets, Business News, Financials, Earnings.
- ^ Kim Boatman. Beware the Rise of Ransomware. Norton Security Center. A Complete Online Security Resource.
- ^ Rick Correa. How Fast Does Ransomware Encrypt Files? Faster than You Think. Barkly Endpoint Security Blog. The latest endpoint security news, tips, and actionable insights.
- ^ Alex Drozhzhin. Why you should NOT pay ransom to malware creators. Kaspersky Blog. Information to help protect you against viruses, spyware, hackers, spam.
- ^ Dan Goodin. An NSA-derived ransomware worm is shutting down computers worldwide. Ars Technica. IT news, reviews, and analysis.





















