14 versions of various Microsoft viruses and scams found on 2021
Microsoft virus Removal Guide
What is Microsoft virus?
Microsoft virus is a term used to describe technical scam campaigns when the name of a company is used to trick people
Microsoft virus is a name of different threats (scams, mostly) that are using the logo of Microsoft Corporation[1] to prove their legitimacy and trust. These malware series appear to be mostly scam applications that appear while browsing and start providing fake security alerts to urge users to call certified Microsoft technicians. Additionally, victims are asked to pay for the help which they don't even need. This is the main reason why crooks decided to misuse the company's name.
Due to the increasing rate of potentially suspicious and malicious infections that have been targetting Windows users via providing them with the original logo, the Corporation itself released a guide on what kind of viruses are spread the most and how to prevent suspicious programs from sneaking into the targeted system.[2] However, the main thing to do is to disable the malicious master.exe or similar file and then reset the web browser.
| Name | Microsoft virus |
|---|---|
| Types | Scams, malicious files |
| Related malware |
|
| Aim | To swindle personal information or money, inject malware on the targeted machine |
| Distribution techniques | Scams can be caused by adware or other potentially unwanted programs, malicious files, e.g. master.exe, often come as attachments to email spam |
| Browsers affected | Microsoft Edge, Google Chrome, Internet Explorer, Mozilla Firefox can be filled with rogue extensions and other helper components |
| Targeted operating system | Windows (all types of versions such as 7, 8, 10, etc.). However, the appearance of malware is more common on Windows 10 as this OS is the most used one nowadays |
| Removal software | Download a tool such as an anti-malware app to detect all malicious entries and potentially unwanted content on your infected machine. After that, opt for the wanted removal method (automatical/manual) |
| Repair | When a malicious program affects the performance of your machine, you need help from PC tools like FortectIntego that can repair altered data |
Microsoft virus is a very wide term that overtakes various PUPs and cyber threats. Usually, cybercriminals deliver scams by misusing this name. Such rogue applications are also known as technical support scams.[3] By providing fake information on supposedly infected computers, hackers trick users into calling the given mobile phone number.
If the victim decides to make a call via the provided fake technical support number, anything can happen. Once users are connected with fake help experts, they might be urged to provide some personal details about themselves or be convinced to install rogue repair software. As you can see, this type of virus might be spread for very tricky purposes.
If you encounter fake notifications via your browser urging you to call certified Microsoft technicians, make sure not to dial the fake phone number as revealing personal information might relate to data theft in the future. Also, cybercriminals might find a way how to remotely gain access to your computer system if you reveal some crucial details to these people.
Instant removal is the best thing to do once infected with malware or a PUP. If it is a scam which has been lately triggering your normal work, there supposedly is an adware program on your computer system or another suspicious application that has been forcing the scam message to appear whenever browsing the Internet.
You can use the help of SpyHunter 5Combo Cleaner, Malwarebytes to locate malicious or suspicious content on the infected machine. This should help you to remove virus from your Windows OS. By the way, do not be surprised if you find some rogue content in web browser applications such as Chrome, Edge, Explorer, and Firefox that needs to be eliminated too.
However, there might be other more dangerous malware forms lurking under the name of Microsoft. For example, in 2018 there were reports released that malicious payload (which includes ransomware viruses and dangerous Trojan horses) was delivered through infectious Microsoft Office documents and files.
Spotting dangerous infections, especially trojan and ransomware-based ones, signifies possible system damage. These types of Microsoft viruses are the rarest but the most dangerous ones. Such infections can relate to theft of personal information, money swindling, permanent damage of crucial computer software, system resource overuse.
For further information, these versions are carried via infected documents that come attached to email spam. It is very important to scan all received email messages together with attached files in case some malicious objects are hidden there. Better be too cautious than not careful at all.
Most popular versions of Microsoft virus. As of 2021 we list 14 versions
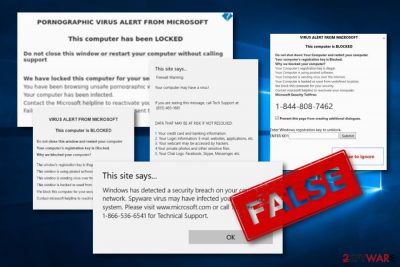
PORNOGRAPHIC VIRUS ALERT FROM MICROSOFT
PORNOGRAPHIC VIRUS ALERT FROM MICROSOFT is considered to be a technical support scam that claims false things such as system damage while visiting pornography-themed websites for receiving calls from users. If you ever get a message from this type of virus and it does not disappear after installing Adblock, there might be adware lurking in your system and forcing the appearance of this scam.
Once PORNOGRAPHIC VIRUS ALERT FROM MICROSOFT scam appears on your computer screen, you will supposedly notice it. The fake message claims that the computer is locked and users need to call the given mobile phone number for help. DO NOT dial this number as hackers might try to swindle your money for useless security software or trick you to provide personal data.
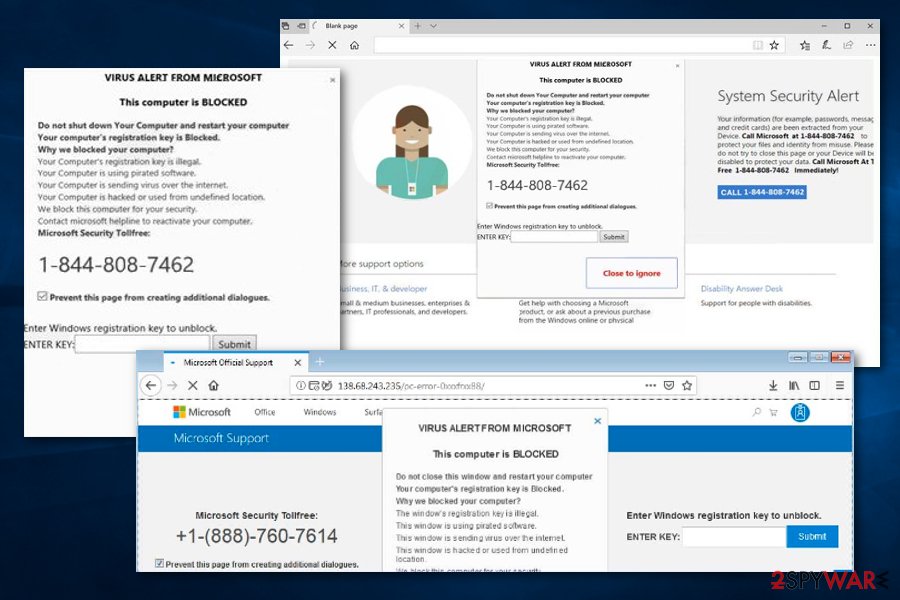
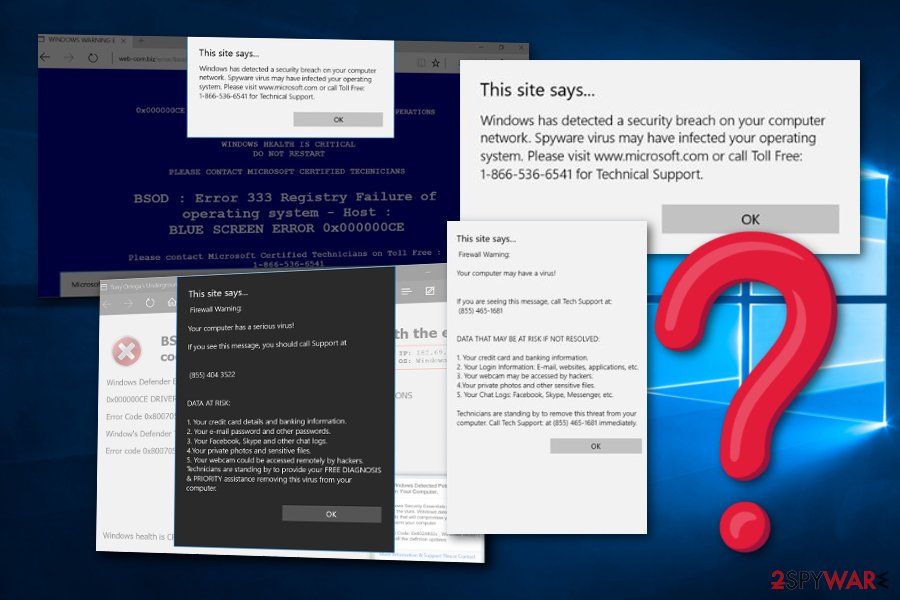
VIRUS ALERT FROM MICROSOFT
VIRUS ALERT FROM MICROSOFT is another scam that is very similar to the previous one. This message also claims that the computer is locked due to a malicious infection and the only way to repair the damage is to contact the fake Microsoft helpline. This technical support number also is another fake one.
If you read the message, you will find that virus scam claims many strange things such as that your computer is spreading malware throughout the Internet sphere, is running third-party programs, has been hacked and that the fake experts have been locking the system for safety. DO NOT believe in such things, these are LIES.
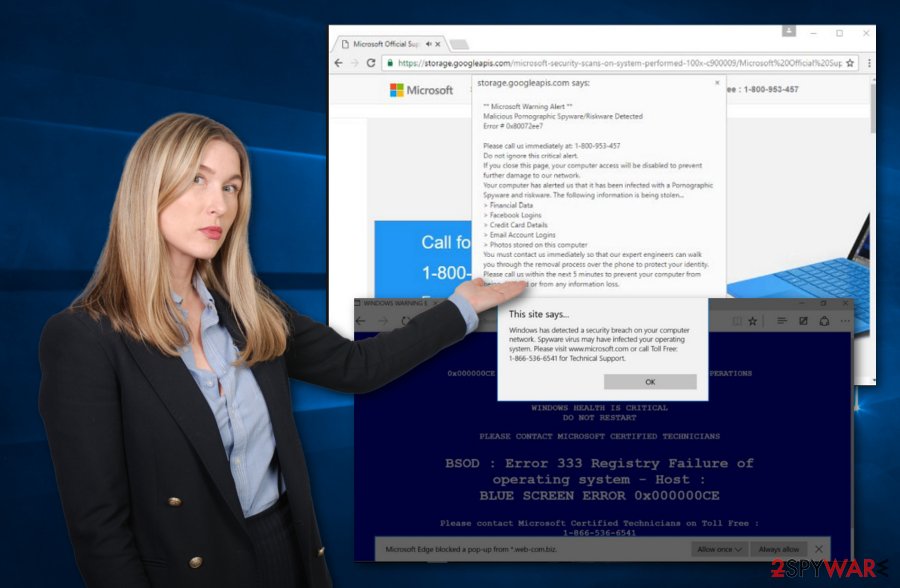
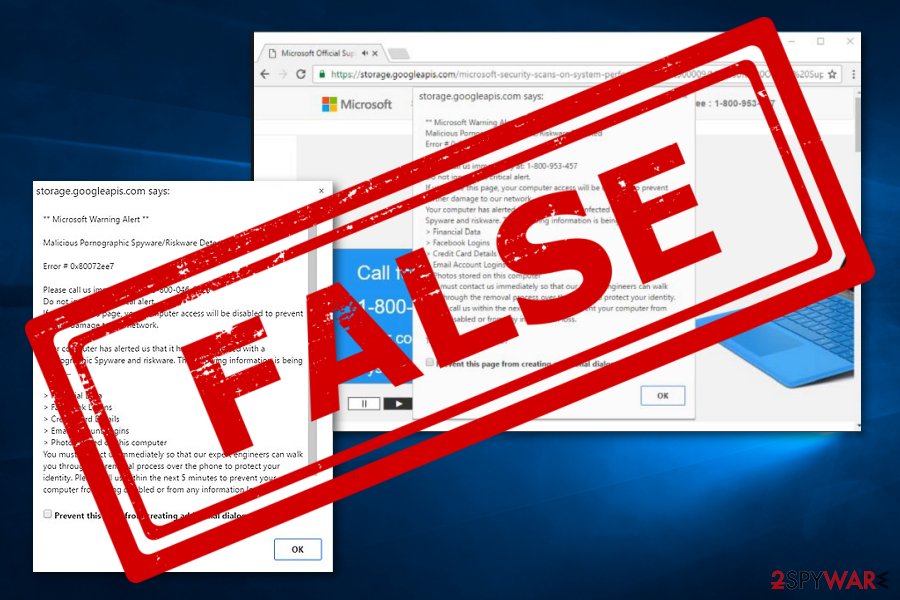
Microsoft Warning Alert
Microsoft Warning Alert is a technical support scam. The fake scam message provides a “critical alert” that urges users to contact the 0-800-046-5729 mobile phone number for instant help. Hackers claim that if the alert window is closed, computer connection and system work will be disabled.
Continuously, these cybercriminals keep on lying further. They claim that such damage and errors appeared due to pornographic spyware and riskware. However, the true risk while dealing with virus that you should worry about is calling the fake helpline which can try to swindle personal information about you or your system for malware exploitation.
Microsoft Edge virus
Microsoft Edge virus is considered to be potentially unwanted content that aims to scare people for receiving benefits. The warning message appears as a Firewall alert and states that various data is at risk due to the secret infiltration of a computer virus. Calling the helpline is claimed to be the only way to avoid possible information exposure.
If you ever receive a message, do not fall for believing in its claims. The note states that data such as credentials, banking information, Facebook and Skype logins, various passwords, and email addresses can be easily leaked if the problem is not fixed immediately.
Besides, the crooks threaten people via the fake Edge virus message that their private photographs and video clips can be leaked. Nevertheless, potential criminals might have the ability to remotely access the webcam. Warning: do not fall for believing this as the only crooks are the people who have been providing this message.
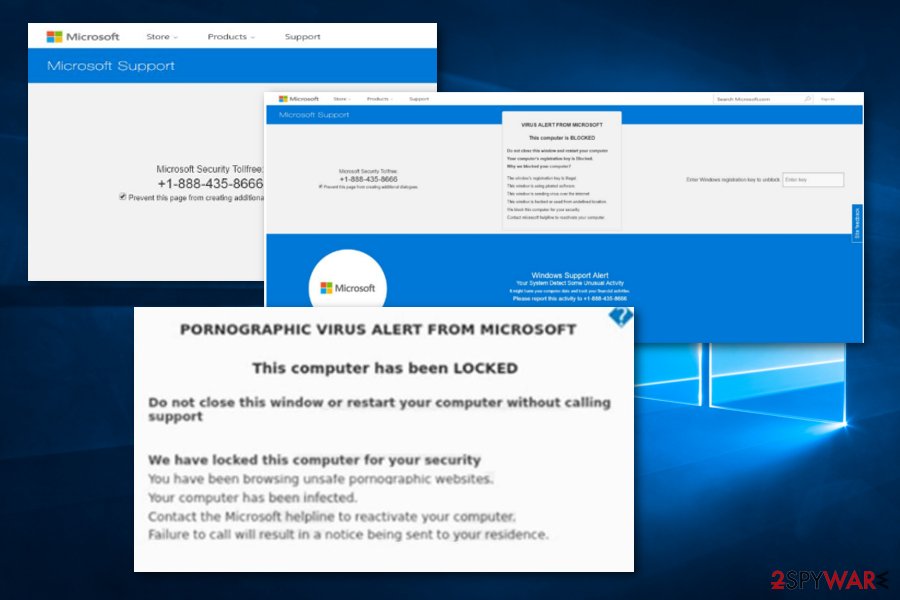
“Microsoft Critical Alert”
“Microsoft Critical Alert” appears to be another scam app that misuses the original name of Microsoft Corporation. Scamming and tricking users into dialing the given Technical Support number 1-855-813-2335. The suspicious notification claims about a Windows System Alert, that the computer system has been infected and blocked.
Furthermore, the crooks announce that the only way to remove the error and unblock the computer system is by calling the tech support. However, we recommend NOT to provide any relevant or true information. You might be tricked by scammers into revealing personal information when talking with the developers on the mobile phone.
Microsoft Security Essentials Alert virus
Microsoft Security Essentials Alert virus, also known as Hicurdismos, is also another technical support scam. This misleading notification appears while an infectious executable monitors malicious processes in the background. Once users are tricked to install and open a file named “setup.exe”, the virus provides a false BSoD error screen.
Note that legitimate BSoD errors usually disappear after rebooting the computer system. However, crooks behind the scam urge to call the fake Support helpline (1-800-418-4202) in order to receive some information on how to solve the problem. No contact should be made with these scammers even though they will try to create a legitimate look of the error.
Scammers can monitor some different actions just to try to convince users that the problem truly does exist. These types of activities include disabling all processes in the Task Manager section, covering the entire screen with the BSoD error and denying access to any apps, and hiding the mouse cursor.
Your Windows (Microsoft) Computer has been blocked
Your Windows (Microsoft) Computer has been blocked is a misleading message that frequently targets Windows users. This notification also claims false things to trick users into calling the provided helpline number. First of all, the rogue message states that the system includes an error and that browsers might be hijacked.
Nevertheless, scam app becomes even scarier when the message alerts about the potential danger of private data and credentials. You can read that credentials and banking data, email logins, Facebook and other popular networks' logins, and private videos are at risk of exposure.
Microsoft Corporation has blocked your PC
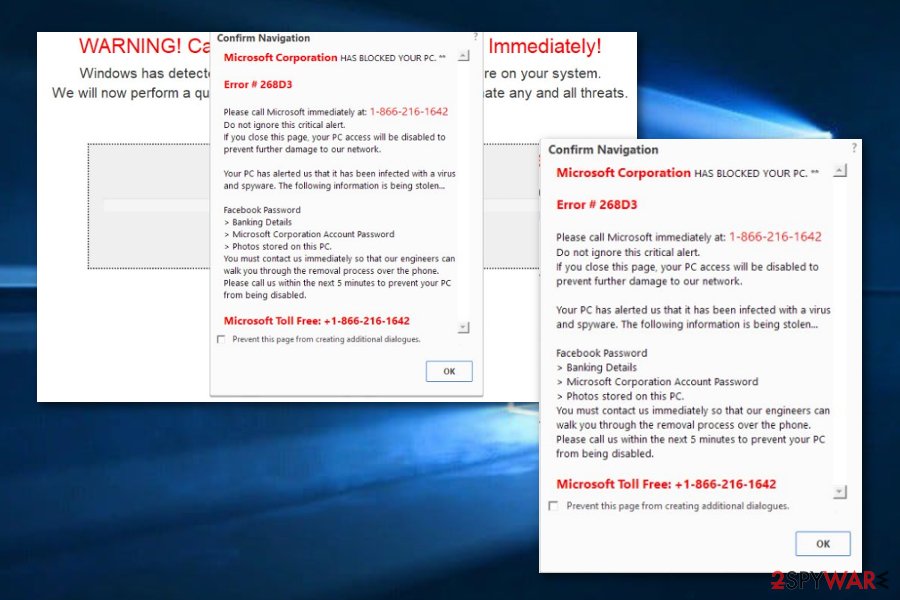
Microsoft Corporation has blocked your PC belongs to the potentially unwanted program, scareware, and technical support scam categories. All of these links are because of the messages misleading content that aims to trick people and also because of its questionable appearance on web browsers.
The claims of scams are very similar to other scam messages. It starts tricking users that there is possible system damage that might relate to sensitive data exposure of components such as passwords, banking information, and pictures that are kept on the falsely infected machine.
As a fixing solution, the hackers provide a Toll-Free number that is claimed to help fix all issues. Calling these people is not an option. Note that such tricky messages can be met anywhere, especially while visiting third-party sources. What you have to do is get rid of all potentially unwanted content from the system.
Microsoft Error: Unknown System Failure
Microsoft Error: Unknown System Failure is considered to be scareware and scamware that infiltrates systems via adware applications or other potentially unwanted programs. The main goal of this questionable message is to provoke users to call fake technical support and try to swindle money for rogue security tools or personal information.
Note that avoiding viruses is the best thing you can do. If the suspicious notification appears only on particular unprotected websites, closing the browser window and never entering that web page again might be what you need for preventing the repeated appearance of the scam.
Microsoft has detected suspicious activity
Microsoft has detected suspicious activity is a technical support scam that operates by using the same principle just like other scam apps. Hackers pretend to be Microsoft support and announce questionable activities happening on the user's computer system. These people also report false attempts to steal sensitive information and banking details.
No trust can be found in this scam application. It is just a scam that bothers you to swindle the personal data and the money. The removal process might include anti-malware tools or manual steps. However, just do not forget to get rid of the adware or another PUP that is provoking this scam to appear.
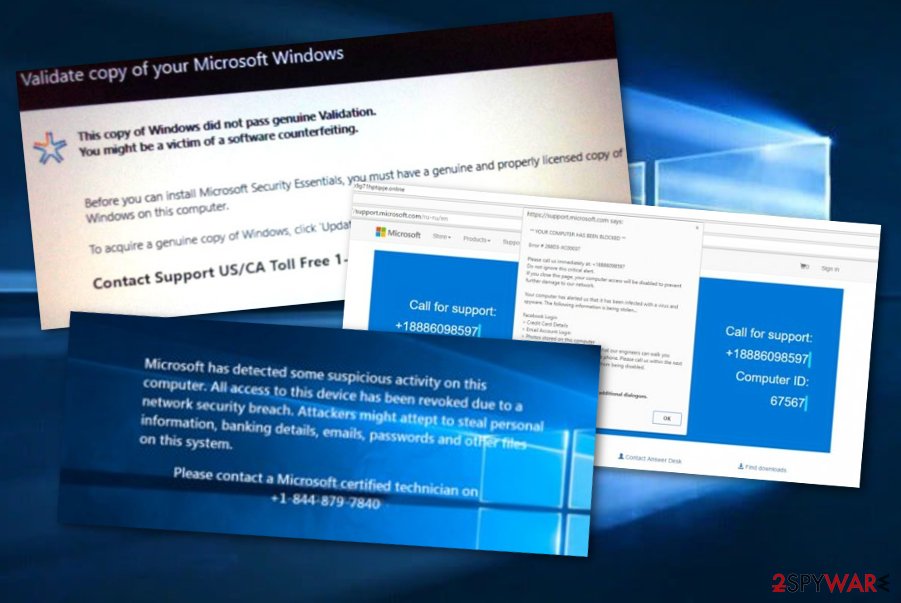
Validate copy of your Microsoft Windows
Validate copy of your Microsoft Windows – a technical support scam which claims that a certain copy of Windows did not pass genuine validation. In order to receive the original copy, users are urged to click on the “Update Now” button and dial the free support number for further help.
However, we recommend neither clicking on the button nor dialing the fake number as this might put you into some trouble. For example, you might be urged to pay for some fake licensed security software or provide sensitive details about yourself and the computer. Get rid of the adware and the notification flow should end.
Microsoft.windowssupport0901.online
Microsoft.com-input11.info
Microsoft.com-input11.info pop-up ads appear when scamware starts attacking the computer system. These types of notifications can be met on third-party networks or be provoked by adware programs. Once the scam ends up on the victim's machine screen, it starts claiming about the false browser and computer danger.
Furthermore, +1-844-313-5529, +1-800-610-8993, +1-866-507-946, or +1-855-336-5598 mobile phone numbers are provided as a way to contact the technical support specialists. You should not fall for believing in these fake claims as none of these errors are true. You can figure that out by scanning the entire system with anti-malware.
Microsoft account password reset email
Microsoft, just like any other organization, uses security measures in order to prevent account theft. It is also not a secret that malicious actors oftentimes send fake emails to make users click on deceitful links and enter their login credentials or download malicious software on their devices.
In the past few months, users have been receiving what seems to be not requested Password reset emails, which seems to come repeatedly. It claims:
Please use the following security code for the Microsoft account (email).
Security code: XXXXXXX
If you don't recognize the Microsoft account (email), you can click here to remove your email address from that account.
While the activity might initially seem very suspicious, it most likely means that somebody is trying to add another email to your account or is trying to gain unauthorized access to it. If you have not requested a password reset email, you should never proceed with using the code provided.
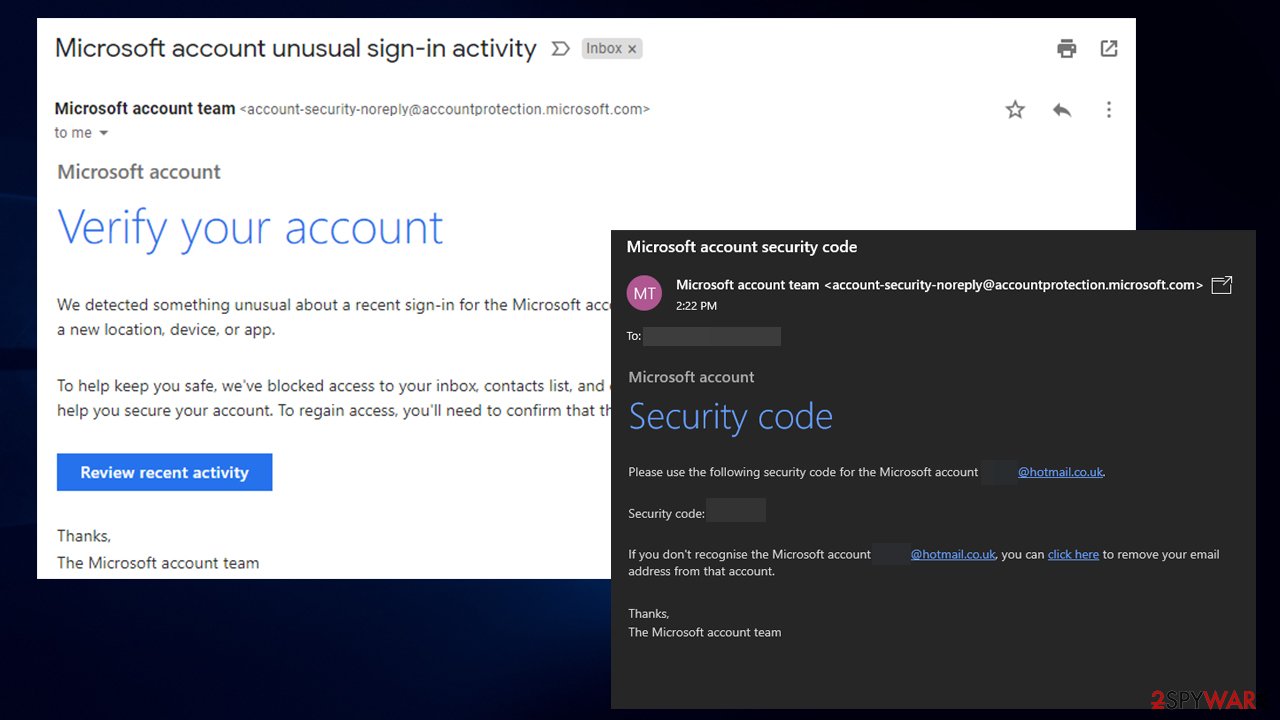
To find out whether password reset email is a scam, you should make several checks. If the email is coming from account-security-noreply@accountprotection.microsoft.com, the email is genuine, as it is a legitimate Microsoft email. The reason you might have received such a message is that you tried to log in via another IP, or when using a VPN, and Microsoft flagged this activity as suspicious.
On the contrary, the “From” address can be easily spoofed, and the contents of the email are forged. Therefore, each individual case requires a deeper examination. To ensure your account security, you should not ignore the Microsoft password reset email. Sign in to your account and initiate the password change yourself. Here's how to do it:
- Go to account.microsoft.com
- Under Security section, pick Update
- Select Change my password
- Enter your current password and a new password
- Click Save.
To conclude, password reset email might be real, but you should never click on links on emails you did not request (a password change).
More danger comes through infected Office files
Internet security experts have released a report about infectious Microsoft Office documents that have been lurking out in cyberspace and carrying malware inside. In September 2018, malware-laden Office files were one of the main computer virus distribution techniques that helped the crooks to easily carry malicious software on users' computers.[4]
Malicious macros who have been inserted in these files carried a big variety of threats in the past. The most popular ones were GandCrab ransomware (one of the most widespread file-encrypting threats throughout the entire malware history), AZORult Trojan horse, Chanitor, and Geodo[5] malware forms.
Infectious but legitimate-looking Office documents are spread by using one of the most popular malware distribution techniques – email spam. Such infected macros are attached to a rogue email message and are executed within one click. After that, the malicious payload can successfully be planted on the targeted machine.
Distribution sources and prevention tips (PUPs)
According to technology and virus specialists from Virusai.lt,[6] potentially unwanted programs are capable of spreading via different types of third-party sources and software bundles. Talking about bundling, you can prevent such activity by using reputable sources for your downloads and opting for the Custom configuration mode.
Continuously, you should be aware of suspicious content such as advertisements and hyperlinks that you might meet while browsing throughout the web. If you ever enter a questionable website and you think that it might be infected with some strange malware, e.g Microsoft virus, close it immediately and never return.
Additionally, it is recommendable to carry out regular system check-ups especially after visits to malware-laden pages. If you choose a reputable tool, it will ensure that your computer system is secured 24/7. Also, the more protective features your antivirus includes, the more advanced your machine protection will be.
Microsoft malware removal requires full system cleaning
If the well-known Microsoft name has been misused by a cybercriminal and you have found some type of similar malware on your computer system, you should remove malware from your Windows computer system without any hesitation. The most popular type of these viruses is scam apps which can be caused by adware or another potentially unwanted program.
If you have been receiving dubious messages and alerts that pretend to be from Microsoft, you can get rid of them by using automatic tools for adware elimination or the below-given step-by-step guide. These instructions will help you to perform the removal from your entire Windows operating system.
Furthermore, here you will find how to remove additional components, which are related to the Microsoft virus, from your web browsers. Beware of suspicious apps that, after being approved, can inject rogue extensions, plug-ins, and add-ons into such directories. This includes cleaning browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, and Microsoft Edge.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Microsoft virus. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Microsoft registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Microsoft. Wikipedia. The free encyclopedia.
- ^ How to prevent and remove viruses and other malware. Microsoft. Windows Support.
- ^ Jaspreet Singh. What is Tech support scam?. Quora.com. Relevant questions and answers.
- ^ Alison DeNisco Rayome. Microsoft Office is more dangerous than you think: Docs deliver 45% of all malware. Tech Republic. Articles.
- ^ Sean Michael Kerner. Hackers Celebrate Fourth of July With Geodo Botnet Spam. E-week. Cybersecurity news articles.
- ^ Virusai.lt. Virusai. Security and spyware news.


















